API Security refers to the set of practices and mechanisms used to protect application programming interfaces (APIs) from unauthorized access, misuse, and data breaches. It ensures that only verified users and trusted systems can interact with APIs, while sensitive data remains protected across every connection point.
As organizations increasingly depend on APIs to connect applications, enable automation, and support real-time data exchange, strong API security becomes essential for safeguarding digital ecosystems, maintaining system reliability, and preserving user trust.
API security best practices are no longer optional, they define how secure, scalable, and trustworthy your systems truly are. In fact, studies show that over 80% of all web traffic today flows through APIs, and nearly one in every three security incidents in modern applications is linked to API vulnerabilities. One exposed API key is all it takes to create a silent vulnerability, one that doesn’t fail loudly but slowly opens the door to misuse. In a world where everything is connected, security gaps are rarely dramatic, they are subtle, and that’s what makes them dangerous.
Yet, many organizations still operate reactively, fixing issues after they surface instead of preventing them in the first place. The real shift lies in building proactive habits: controlling access through structured key management, limiting data exposure through masking, and staying aware through continuous monitoring.
In this blog, we’ll break down how API key rotation, PII masking, and audit log monitoring work in practice, and how adopting these consistently can help you build a stronger, more secure system
Security Gaps in Modern Apps: Access Control & Data Privacy Risks
Security doesn’t fail all at once, it breaks down quietly, in the small things we overlook every day.
Small Gaps That Turn Into Big Risks
Security issues rarely begin as major incidents. They start small, an API security that wasn’t configured correctly, a credential that stayed active longer than it should have, or a log that no one reviewed. These moments don’t feel urgent at the time, which is exactly why they are missed. But over time, these small gaps quietly build into real vulnerabilities that are much harder to control later.
The Cost of Overlooking Security in Fast-Moving Systems
In fast-growing ecosystems like Indian ecommerce and logistics, the pressure to move quickly often outweighs the focus on security. Multiple systems, carriers, and integrations are constantly interacting, and data is always in motion. In such environments, even a minor weakness can escalate quickly, leading to data leaks, financial losses, compliance challenges, and ultimately, a loss of customer trust. And once trust is broken, it’s far more difficult to rebuild than to protect.
The Real Problem:
The biggest challenge isn’t the lack of tools or advanced technology. It’s inconsistency in applying API security practices. Many systems are built with strong foundations, but over time, discipline fades. Security becomes reactive instead of proactive. And that shift is where risk grows. Truly secure systems are not defined by how they start, but by how consistently they are maintained.
In the end, it’s not the tools you have that define your security, it’s how consistently you use them.
Essential Security Controls for Modern Applications and Data Security
Strong security doesn’t come from complex systems, it comes from getting the fundamentals right, every single time. In fast-moving environments, it’s often the small, consistent practices that make the biggest difference. When access is controlled, data is protected, and activity is monitored regularly, systems become far more resilient without adding unnecessary complexity.
1. API Key Rotation: Keep Access Short-Lived
API key rotation is the process of regularly updating API keys to prevent long-term misuse or unauthorized access. These keys act as connectors between systems, and if they remain unchanged for too long, they become vulnerable points.
In practice, many systems continue running on the same keys for months without review. Over time, this increases the risk of exposure, especially when teams change or integrations expand. Rotating keys at regular intervals, and during critical events, helps reduce this risk without disrupting operations when done in a phased way.
-
PII Masking: Limit Data Visibility, Not Usability
PII masking is the practice of hiding or partially displaying sensitive personal information to protect user privacy while keeping systems functional. Instead of showing full details, only limited or obfuscated data is visible to users.
In real-world systems, sensitive data often appears across dashboards, support tools, and logs. Without masking, this creates unnecessary exposure. By limiting visibility, while still allowing workflows to function, organizations can reduce both internal and external risks without affecting usability.
-
Two Factor Authentication
Two-Factor Authentication (2FA) is a security mechanism that requires users to verify their identity using two different forms of authentication before gaining access to a system. Instead of relying only on a password, it adds an extra layer of protection, such as one-time password (OTP).
Even if a password is compromised, 2FA ensures that unauthorized users still cannot access the account without the second verification factor. This significantly reduces the risk of data breaches, account takeovers, and unauthorized system access.
Most modern applications and platforms now support 2FA, but its effectiveness depends on proper implementation and user adoption. When enabled consistently across systems, it becomes one of the simplest yet strongest defenses against credential-based attacks.
Building a habit around enabling and enforcing 2FA across all critical systems makes a major difference in overall security posture.
-
Audit Logs: Turn System Activity Into Insight
Audit log monitoring is the process of reviewing system-generated logs to track user activity, detect anomalies, and identify potential security risks. These logs capture actions across systems, from logins to access changes.
While most systems generate logs by default, they are often underutilized. Without regular review, important signals go unnoticed. A consistent monitoring routine helps teams stay aware of what’s happening and catch issues early, before they escalate into bigger problems.
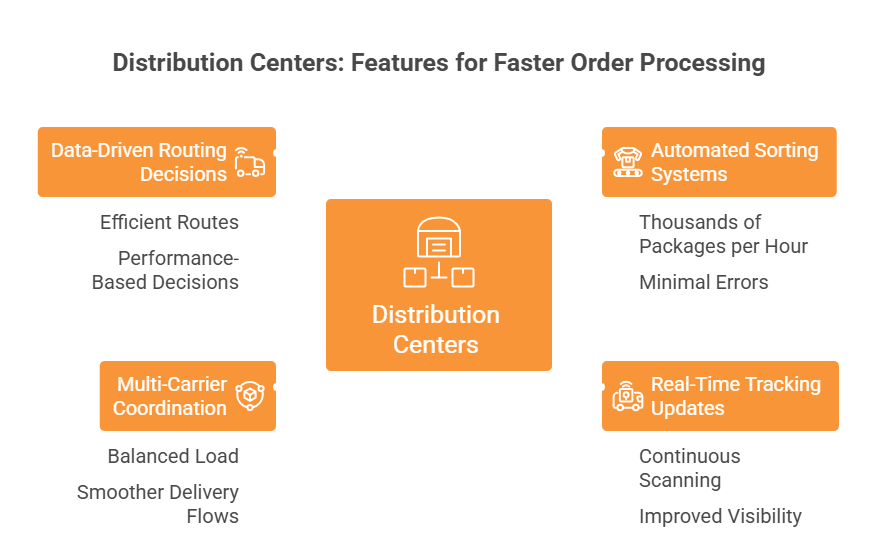
Core Security Controls in eShipz Workflows: Data Protection & Monitoring
Not all security practices solve the same problem. Some focus on controlling access, others on protecting data, and some on identifying risks early. When viewed together, they give a clearer picture of how a system stays secure. Understanding how each practice works, and where it fits, helps teams prioritize better and avoid blind spots.
|
Practice |
Purpose | Risk if Ignored |
Frequency |
| Key Rotation | Prevent credential misuse | Unauthorized system access | Periodic |
| Data Masking | Protect user privacy | Data leaks & compliance issues | Continuous |
| Log Monitoring | Detect suspicious activity | Undetected breaches | Real-time |
In platforms like eShipz, these controls are typically applied as part of the broader shipping automation and integration layer, where multiple carrier APIs, order systems, and tracking services continuously exchange data. For example, API keys used for carrier integrations are rotated periodically to reduce exposure risk, sensitive shipment and customer data is masked across dashboards and reports, and system-level logs are continuously monitored to detect unusual shipment or access patterns across high-volume operations.
Individually, each of these practices adds a layer of protection. But together, they create a more balanced and resilient security approach. The key is not just adopting them, but applying them consistently, so gaps don’t have the chance to grow unnoticed.
Proactive Security Approach: API SEcurity ( Keys) & Access Control Systems
Security risks today are not always complex or highly technical, they often come from small gaps that go unnoticed. In fact, studies show that over 80% of data breaches involve compromised credentials, making them one of the most common entry points for attackers. Additionally, around 60% of organizations report insider-related incidents, often due to excessive or unmanaged access. With the rapid rise of APIs, this risk has only increased, API attacks have grown significantly in recent years, as more systems become interconnected and data flows across multiple platforms.
The challenge is that most teams don’t ignore security, they simply delay it. It often shows up in everyday thinking: “we’ll fix it later,” “it hasn’t caused an issue yet,” or “everything seems to be working fine.” But these small decisions add up. Research indicates that the average time to identify and contain a breach can exceed 200 days, giving attackers a long window to operate unnoticed. At the same time, nearly 70% of breaches are linked to human error or misconfiguration, highlighting how small oversights can lead to larger issues. Without regular checks on access, data exposure, and system activity, risks quietly build in the background until they become harder to control.
A proactive security approach helps break this cycle. It focuses on building simple, consistent habits, like rotating credentials regularly, limiting how much sensitive data is visible, and reviewing system activity on a routine basis. Organizations that adopt these practices tend to perform significantly better, companies with strong security monitoring can reduce breach impact costs by up to 30%. These are not complex changes, but they are effective. Over time, this consistency creates systems that are not just secure, but also stable, resilient, and better prepared for evolving threats.
Security as a Continuous Practice: Credential Security & Monitoring
Security is not something you complete, it is something you continuously strengthen. Many security gaps don’t come from missing controls, but from controls that are not consistently maintained. Even strong systems can become vulnerable over time if they are not regularly reviewed, updated, and enforced as part of daily operations.
In platforms like eShipz, where multiple carrier integrations and high-volume shipment data flows run continuously, this consistency becomes even more important. Ongoing monitoring, controlled access, and careful data handling help ensure that scale does not reduce security visibility or control.
By focusing on controlled access, limited data exposure, and continuous monitoring, organizations can significantly reduce security risks.
The real shift is from reactive fixes to proactive discipline, and in systems like eShipz, that discipline is what keeps operations both scalable and secure.